spyware
-
Virtualization
![🔐🛡️[Domain 2.3] Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities 🔐🛡️[Domain 2.3] Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities](data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI3ODAiIGhlaWdodD0iNDcwIiB2aWV3Qm94PSIwIDAgNzgwIDQ3MCI+PHJlY3Qgd2lkdGg9IjEwMCUiIGhlaWdodD0iMTAwJSIgc3R5bGU9ImZpbGw6I2NmZDRkYjtmaWxsLW9wYWNpdHk6IDAuMTsiLz48L3N2Zz4=)
🔐🛡️[Domain 2.3] Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities
Objective 2.3: Explain various types of vulnerabilities CompTIA Security+ NEW SY0-701 Cybersecurity exam 2025. Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities The Dragon’s fiery breath can destroy entire cities, much like vulnerabilities can devastate our digital infrastructure. In this video, we’ll explore different types of vulnerabilities, including buffer overflows, SQL injection, and cross-site scripting. We’ll also discuss the importance…
Read More » -
VMware

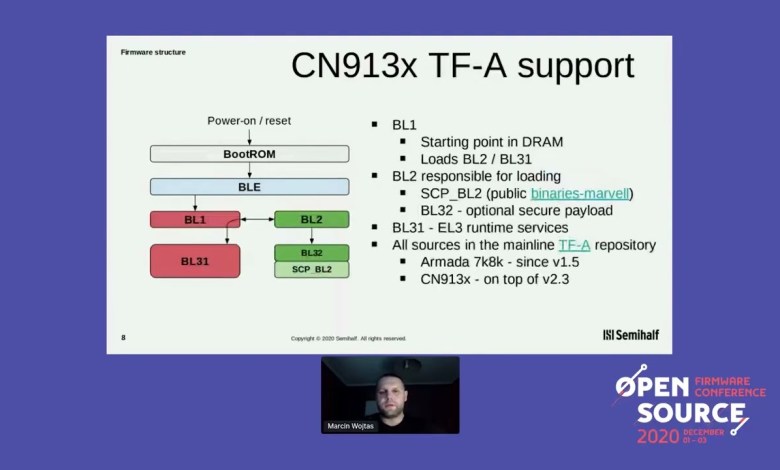
Marvell Octeon TX2 CN913x fully open source firmware Marcin Wojtas
OSFC 2020 Hacking conference #hacking, #hackers, #infosec, #opsec, #IT, #security [ad_2] source
Read More » Mantra OS Because the World is Cruel Gregory Disney Leugers
OWASP – AppSec California 2014 Hacking conference #hacking, #hackers, #infosec, #opsec, #IT, #security [ad_2] source
Read More »Es Windows 11 Windows XP con sobrepeso?
Este video explora la evolución de los sistemas operativos de Windows desde su época dorada con Windows XP hasta la actualidad con Windows 11. Se destaca cómo Windows XP fue el último Windows auténtico, mientras que Windows 11 parece ser una copia con características innecesarias. Se examinan aspectos como el consumo de recursos, la seguridad, la estabilidad y la eficiencia…
Read More »
![🔐🛡️[Domain 2.3] Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities 🔐🛡️[Domain 2.3] Bend The Knee to Cybersecurity: Understanding Common Vulnerabilities](https://wp.fifu.app/howto.goit.science/aHR0cHM6Ly9pLnl0aW1nLmNvbS92aS9memVSbXM5RlVGWS9tYXhyZXNkZWZhdWx0LmpwZw/e50f48f903cb/%f0%9f%94%90%f0%9f%9b%a1%ef%b8%8fdomain-2-3-bend-the-knee-to-cybersecurity-understanding-common-vulnerabilities.webp?w=780&h=470&c=1&p=642533)