network security
-
VMware

Johnson Controls Cyber Attack Explained: Impact and Mitigation Strategies
The recent cyberattack on Johnson Controls has a lot of people concerned and many organizations wondering what they need to do to help secure their networks. In this video we give a brief overview of what has happened and what is currently known about the incident. We also talk about a few steps taken to help keep network data safe.…
Read More » -
VMware

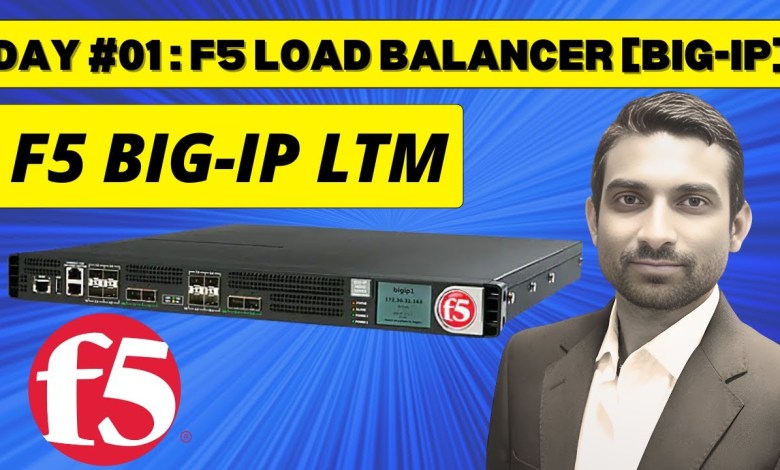
F5 Load Balancer || Day 1: F5 BIG-IP LTM Training
#loadbalancer #itnetworking #imedita Welcome to I-MEDITA’s in-depth training series on F5 Load Balancers! In this video, we kick off Day 1 of our comprehensive F5 BIG-IP Local Traffic Manager (LTM) training. Whether you’re a network engineer, system administrator, or IT professional looking to enhance your skills, this series is designed to provide you with a thorough understanding of F5 load-balancing…
Read More » -
VMware

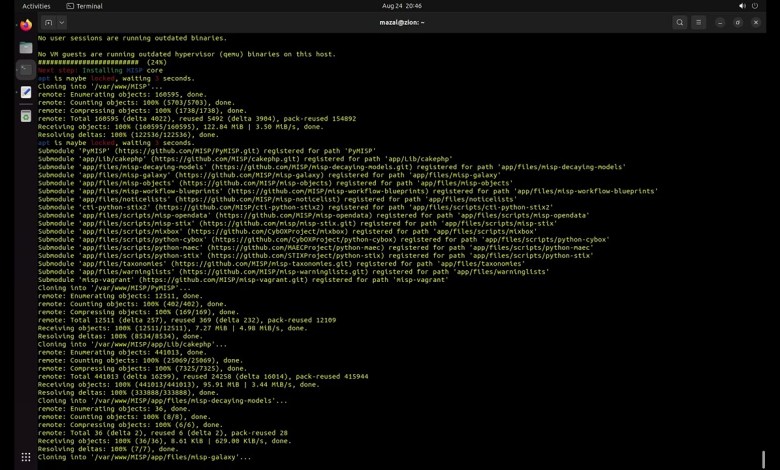
How to Install MISP on Ubuntu Server 22.4. (KDE Ubuntu Desktop)
Welcome to our comprehensive tutorial on installing MISP (Open source Threat Intelligence and Sharing Platform) on Ubuntu Server 22.4 with KDE Ubuntu Desktop. In this step-by-step guide, we walk you through the entire installation process to set up MISP for threat intelligence management and sharing. 🔗 Links and Resources 🔗 – MISP Official Website: [ – Ubuntu Server 22.4 Download:…
Read More » -
Linux

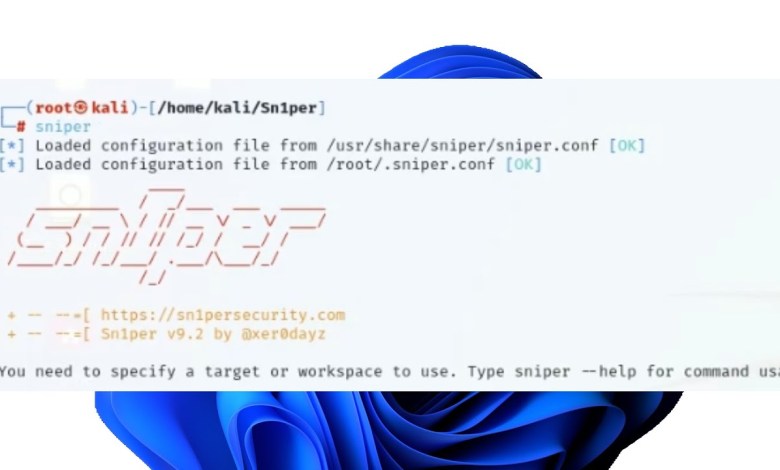
How to Install Sn1per on Kali Linux | Cyber Security Ep 2
Welcome to our comprehensive guide on installing Sn1per on Kali Linux! 🚀 In this video, we will walk you through the entire process of installing Sn1per, a powerful automated pentesting scanner, on your Kali Linux system. Sn1per is an essential tool for cybersecurity professionals and enthusiasts, helping to streamline the reconnaissance and vulnerability assessment phases of penetration testing. What You’ll…
Read More » -
VMware

Critical VMware ESXi Hypervisor Vulnerability
The conversation discusses a vulnerability in VMware ESXi hypervisors that grants full admin privileges to threat actors. The vulnerability has been exploited by ransomware groups to deploy ransomware after gaining access to a network. The hosts emphasize the importance of patching systems and working with security teams or MSP/MSSPs to address the vulnerability. They also highlight the need for better…
Read More » -
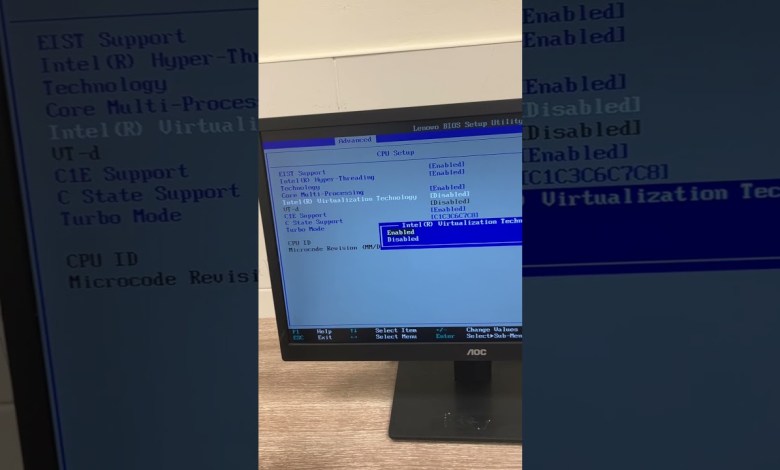
Virtualization

VMware Virtualization error
VMware Virtualization error If you try to install an operating system to windows and you get an error just like below [ad_2] source
Read More »