it security
-
Linux

| INTRODUCTION | How to Install BURP SUITE on Kali Linux and VirtualBox | Web App Pen testing.
Burp Suite is a software tool, primarily used on an Operating System like Kali Linux, for security assessment and penetration testing of web applications. Many web apps and sites have weakness or vulnerabilities and Burp Suite is very powerful at exposing these. Some of its uses are shown below: – Mapping and analyzing: Mapping an application’s attack surface and analyzing…
Read More » -
Virtualization

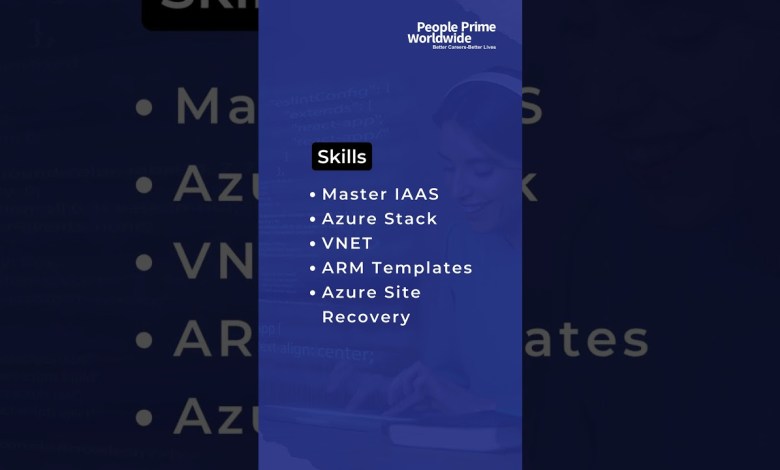
IT Infra Jobs: Azure IaaS Admin Wanted! | People Prime IT Infra Jobs
Are you passionate about cloud technology and ready to advance your career? People Prime Worldwide is seeking a skilled Azure IaaS Admin. You’ll manage and optimize Azure infrastructure in this role, ensuring smooth operations and security. If you’re an expert in Azure IaaS with a knack for problem-solving and innovation, this opportunity is perfect for you! Would you be ready…
Read More » -
Virtualization

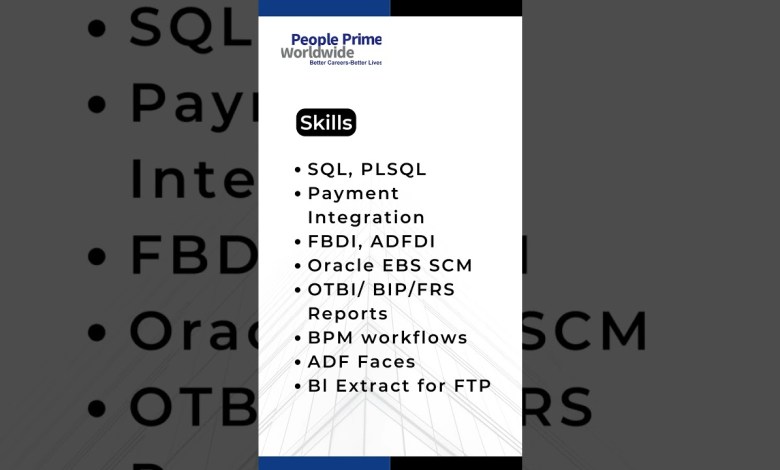
IT Infra Jobs: Oracle EBS SCM Technical Consultant Wanted! | People Prime IT Infra Jobs
Are you an Oracle EBS SCM expert looking for your next career challenge? In this role, you’ll design, develop, and implement Oracle EBS SCM solutions, ensuring seamless supply chain management for our clients. Work alongside industry leaders, tackle exciting projects, and advance your career with continuous learning opportunities. If you’re passionate about technology and ready to make an impact, apply…
Read More » -
Virtualization

IT Infra Jobs: Network SME Engineer Wanted | People Prime IT Infra Jobs
Elevate your IT career with People Prime Worldwide! We’re looking for a Network SME Engineer. If you’re passionate about network design, implementation, and management, this is your chance to shine. As a Network SME Engineer, you’ll handle complex network solutions, ensure optimal performance, and collaborate with experts in the field. Ready for a challenging and rewarding role? Apply now to…
Read More » -
Virtualization

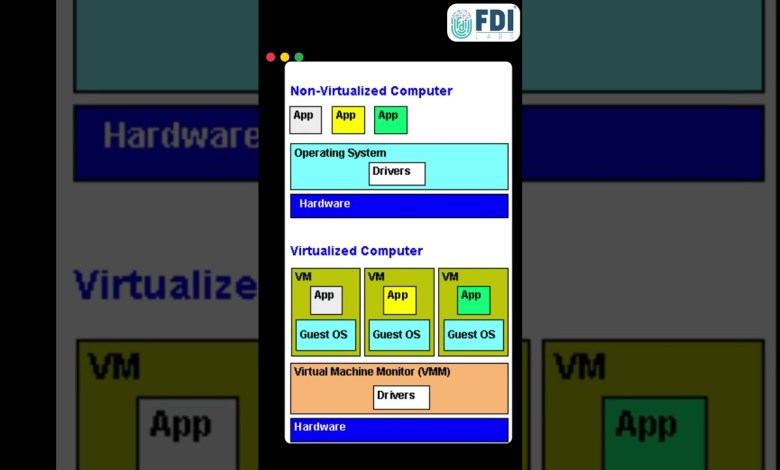
Pros and Cons of Virtual Machines
Virtual machines (VMs) offer numerous advantages, including resource efficiency by allowing multiple operating systems on one physical machine, thereby reducing hardware costs. They provide strong isolation and security, ensuring independent application environments, and scalability to easily match workload demands. VMs facilitate disaster recovery with quick backups and restorations and support cross-platform compatibility, allowing different OSs on the same hardware for…
Read More » -
VMware

Johnson Controls Cyber Attack Explained: Impact and Mitigation Strategies
The recent cyberattack on Johnson Controls has a lot of people concerned and many organizations wondering what they need to do to help secure their networks. In this video we give a brief overview of what has happened and what is currently known about the incident. We also talk about a few steps taken to help keep network data safe.…
Read More »