information security
-
Proxmox

🔴 Oct 18’s Top Cyber News NOW! – Ep 732
The stories that matter most to #cybersecurity insiders, analysts, and business leaders. Delivered every day. Check out Barricade Cyber for #incidentresponse, #ransomware protection, and business recovery services: Allow what you need, block everything else… Including ransomware. Zero trust Endpoint Protection Platform at Check out John Strand’s Pay What You Can Antisyphon Training: Get my GRC Analyst Master Class, packed with…
Read More » -
VMware

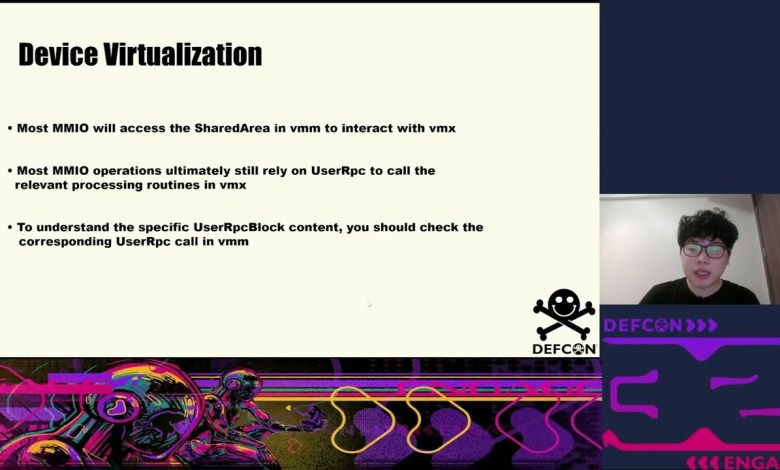
DEF CON 32 – Bug Hunting In VMware Device Virtualization – JiaQing Huang, Hao Zheng, Yue Liu
In this presentation, we will unveil a new attack surface: Device Virtualization in VMKernel. This isan unknown territory that has not been explored by security researchers to date. During the reverse engineering of the VMware Hypervisor, we discovered 8 vulnerabilities related to device virtualization, 3 of them have been assigned CVE number (some vulnerabilities have even been successfully exploited in…
Read More » -
VMware

WinRAR Exploited To Encrypt Windows & Linux – New Ransomware Strategy?!
Researchers have uncovered a critical vulnerability in the widely used WinRAR tool that hackers are exploiting to deploy ransomware across both Windows and Linux systems. In this video, we dive into how hacktivist group Head Mare is using this flaw, known as CVE-2023-38831, to encrypt data, targeting industries in Russia and Belarus with sophisticated ransomware like LockBit and Babuk. We’ll…
Read More » -
Linux

I Installed Kali Linux NetHunter on Android in 10 Minutes WITHOUT Root
In this video, we will guide you through the process of installing Kali NetHunter on your Android device in just 10 minutes, and the best part? No root is required! Kali NetHunter is an advanced penetration testing platform that turns your Android device into a powerful security testing tool. Whether you’re a beginner or an experienced hacker, this step-by-step tutorial…
Read More » -
Linux

#2 How to build a HACKING lab : Install Kali Linux in Minutes!
🚀 Welcome to Your Hacking Journey! 🚀 In this video, we’ll guide you through the entire process of installing Kali Linux—the go-to operating system for ethical hackers and cybersecurity professionals. Whether you’re a complete beginner or looking to refresh your skills, this tutorial is designed to be straightforward and easy to follow. 🌐 Why Kali Linux? Kali Linux is equipped…
Read More » -
workstation

Cyber Security tutorials || Demo – 4 || by Mr. Shoaib Ahmed On 26-09-2024 @9:15PM IST
Cyber Security tutorials || Demo – 4 || by Mr. Shoaib Ahmed On 26-09-2024 @9:15PM IST Course Content: ====================================================================== To get latest DURGASOFT updates on trending Technologies, Please Subscribe to Our Telegram Channel: LINK: ==================================================== You an see more Java videos following link: Java tutorial by durga sir Java 9 by durga sir Java 1.8 Version New Features by Durga…
Read More »