exploit
-
VMware

WinRAR Exploited To Encrypt Windows & Linux – New Ransomware Strategy?!
Researchers have uncovered a critical vulnerability in the widely used WinRAR tool that hackers are exploiting to deploy ransomware across both Windows and Linux systems. In this video, we dive into how hacktivist group Head Mare is using this flaw, known as CVE-2023-38831, to encrypt data, targeting industries in Russia and Belarus with sophisticated ransomware like LockBit and Babuk. We’ll…
Read More » -
VMware

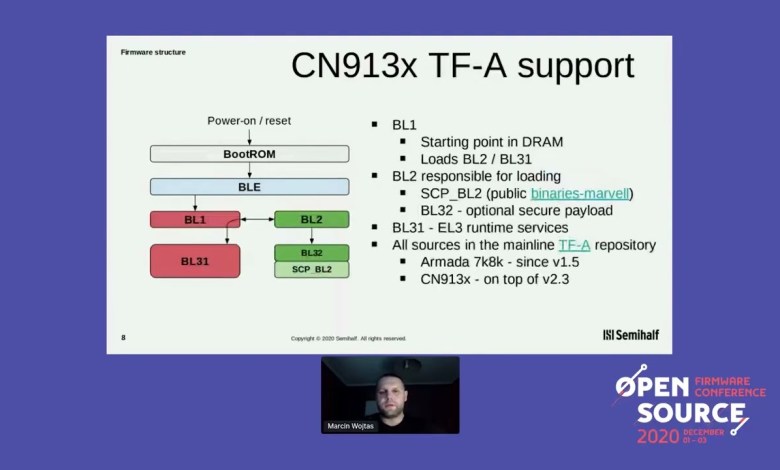
Marvell Octeon TX2 CN913x fully open source firmware Marcin Wojtas
OSFC 2020 Hacking conference #hacking, #hackers, #infosec, #opsec, #IT, #security [ad_2] source
Read More » PS4 Jailbreak 11.00 fix – “scanning for corrupted object” – error
In this video, I’ll share my breakthrough in fixing the PS4 exploit on 11.00 firmware that often fails during the jailbreak process. (Sponsored By PCBWAY: ), After facing 30+ attempts with “scanning for corrupted object” failing every time, I discovered a specific step that improved my success rate to 90% (9 out of 10 attempts). Join me as I walk…
Read More »Mantra OS Because the World is Cruel Gregory Disney Leugers
OWASP – AppSec California 2014 Hacking conference #hacking, #hackers, #infosec, #opsec, #IT, #security [ad_2] source
Read More »How to install Zphisher offline in Kali linux 2019
#Zphisher #alfa #kali #offline # Zphisher is a sophisticated and potent tool in the realm of cybersecurity, designed to simulate phishing attacks with remarkable accuracy and efficiency. It stands as a testament to the evolving landscape of cybersecurity, where both defenders and attackers continuously innovate in a perpetual cat-and-mouse game. At its core, Zphisher operates as a phishing toolkit, allowing…
Read More »🔒 Exploit Ransomware Attacks: Unpacking VMware ESXi Vulnerabilities in 2023! 🔒
: 🚨 **Discover How Hackers Exploit VMware ESXi in 2023!** 🚨 🔑 In this detailed analysis, we dive deep into the recent surge of ransomware attacks targeting VMware ESXi vulnerabilities. With expert insights and real-time demonstrations, learn how these exploits are conducted and the critical steps you can take to safeguard your systems. 🛡️ **What You Will Learn:** – 🧠…
Read More »