DataProtection
-
Windows

Microsoft、Windows 11でTPM 2.0を必須要件に据える理由【自作PC】
ご視聴有難うございます❗️ 高評価とチャンネル登録をお願いいたしますペコリ(o_ _)o)) ご感想もコメントいただけると嬉しいです😃 ▼チャンネル登録はこちらから❗️ ▼毎日夜にまとめ動画も定期投稿しています(サブチャンネル)🫡 ▼Xもやってます❗️ ▼参考 ▼立ち絵 坂本アヒル ▼立ち絵_haira式_サイドテール琴葉茜(PSDToolKit対応) ▼A.I.VOICE 琴葉茜葵 結月ゆかり 紲星あかり ▼VOICEVOX 雨晴はう 春日部つむぎ 四国めたん ずんだもん whiteCUL 小夜 ▼SE/BGM 効果音ラボ: OP – A Serenade to Veracruz / Jimena Contreras MAIN – Final Girl / Jeremy Blake ED – You and Me / しゃろう 0:00 開始 0:11 導入 0:34 TPM 2.0の概要と重要性 1:24 セキュリティ強化の具体的な効果 2:10 TPM 2.0の導入が必要な理由 2:54 今後の展望と課題 #tpm #ティーピーエム #windows11 #ウィンドウズイレブン #secureboot #セキュアブート #bitlocker #ビットロッカー #microsoft #マイクロソフト #security #セキュリティ #encryption #エンクリプション [ad_2] source
Read More » -
VMware

Fortinet – FortiGate VM Download
#NetworkSecurity #CyberSecurity #InfoSec #DataProtection #SecurityAwareness #EthicalHacking #CyberSecurityTraining #Firewall #ITSecurity #NetworkDefense #SecurityBasics #DataPrivacy #ThreatHunting #MalwareProtection #SecureNetwork #CyberAwareness #SecurityTips #NetworkEngineer #DigitalSecurity #CyberThreats Fortinet – FortiGate VM Download Fortinet – FortiGate VM Install Fortinet – FortiGate License Registration Fortinet – FortiGate Initial Configuration Fortinet – FortiGate Interface Configuration [ad_2] source
Read More » -
Linux

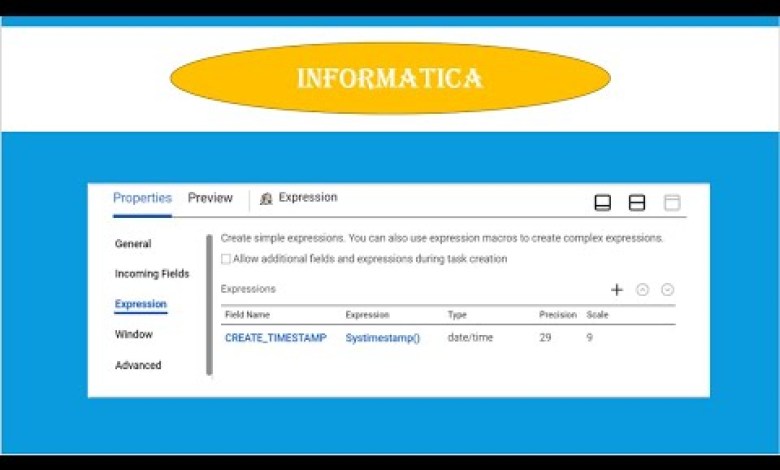
| Shrimanii | Expression Transformation Errors | Solution | Error Fixed | Informatica | ICS | IDMC
Expression Transformation in informatica Lear how to create/test/fix Expression transformation errors ……. | Trial account | Expression Transformation Errors | Solution | Error Fixed | Informatica | ICS | IDMC #Query Solved – Create Trial account – Create sample mapping – Create FlatFile Connection – Using Expression transformation – Using Sorter transformation – Using Joiner transformation – Using Filter transformation…
Read More » -
CWP panel

AI in the Hand of the Cyber Protectors-by Tal Shapira-Why 2024 will become the Year of SaaS Security
AI in the Hands of the Cyber Protectors’ – by Tal Shapira – Why 2024 will become the Year of SaaS Security Meetups Welcome to the virtual meetup that unveils the pivotal role of SaaS security in the cloud landscape of 2024. With data-driven products rapidly advancing and IT resources evolving for greater efficiency, the need to fortify against cyber…
Read More » Unveiling Eldorado Ransomware: A New Threat Targeting Windows and VMware ESXi Systems
Emergence of Eldorado Ransomware Overview: A new ransomware-as-a-service (RaaS) called Eldorado has surfaced, targeting both Windows systems and VMware ESXi virtual machines. This threat is notable for its capacity to encrypt large networks and demand substantial ransoms. Key Details: • Capabilities: Eldorado ransomware has the ability to encrypt data on both Windows systems and VMware ESXi virtual machines, which are…
Read More »Unlock Anonymous Browsing: Tails OS The Ultimate Guide Private Internet Access #fyp #fypage #shorts
Unlock Anonymous Browsing: Tails OS – The Ultimate Guide to Secure, Private Internet Access #fyp #fypage #shorts Are you concerned about your online privacy and security? Want to browse the internet without leaving any trace? Look no further! In this comprehensive guide, we dive deep into the world of Tails, the amnesic incognito live system designed to keep your activities…
Read More »