CyberSecurity
-
Proxmox

🔴 Oct 18’s Top Cyber News NOW! – Ep 732
The stories that matter most to #cybersecurity insiders, analysts, and business leaders. Delivered every day. Check out Barricade Cyber for #incidentresponse, #ransomware protection, and business recovery services: Allow what you need, block everything else… Including ransomware. Zero trust Endpoint Protection Platform at Check out John Strand’s Pay What You Can Antisyphon Training: Get my GRC Analyst Master Class, packed with…
Read More » -
Virtualization

What is a Virtual Machine and Why Do We Need It? | Beginner’s Guide to Virtualization
In this video, we dive deep into the concept of virtual machines (VMs) and why they are essential in today’s tech world. Whether you’re a beginner or an advanced user, understanding virtual machines can greatly enhance your ability to create isolated environments for testing, development, and more. We’ll explain how VMs work, why they are important for penetration testing, software…
Read More » -
workstation

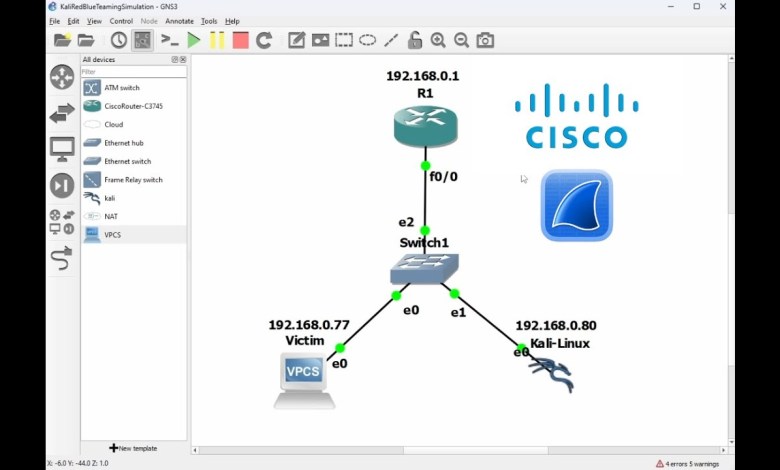
GNS3 Lab Setup: Network Packet Analysis Simulation with Wireshark,Kali Linux,Cisco Router
Timeline: 00:00:00 Introduction(Setting up GNS3) 00:27:56 Setting up GNS3-VM for GNS3 Infastructure to work 00:49:23 Setting Up GNS3-Image on Vmware-workstation 01:31:40 Enabling GNS3-VM 02:14:23 Importing & Installing Custom Router 02:36:55 Router-Repository For Downloading Router-Images 02:54:11 Installing & Adding Router to GNS3 04:04:35 Importing & Installing Kali Image on GNS3 04:49:49 Setting Up Configuration of the Router for Kali to work…
Read More » -
Virtualization

Linux for Ethical Hackers Full Course | Linux Ethical Hacking Course | Ethical Hacking | Simplilearn
🔥CISM Certification: Certified Information Security Manager – 🔥MIT – Post Graduate Program in Cyber Security – 🔥Professional Certificate Program in Cybersecurity- Red Team (India Only) – 🔥IIITB – Advanced Executive Program in Cybersecurity (India Only) – 🔥Caltech Cybersecurity Bootcamp – In this video on Linux for ethical hacking, we will take a tour of small Linux full course covering all…
Read More » -
Virtualization

Security Controls – CompTIA Security+ SY0-701 in 4 Minutes
Understanding the 6 Types of Security Controls in CompTIA Security+ (SY0-701) Cybersecurity What are the 6 Types of Security Controls in CompTIA Security+ (SY0-701)? 🤔 In the ever-evolving world of cybersecurity, understanding various types of security controls is crucial—especially for those studying CompTIA Security+ (SY0-701). Just like a skilled doctor uses different treatments depending on the nature and stage of…
Read More » -
VMware

Ransomware Rewind – Ransomware as a Service (RAAS)
Ransomware as a Service or RAAS is a troubling trend. 10 years ago scammers had to have at least a coding background to utilize malware. Not anymore. Now anyone can get their hands on ransomware malware in a few clicks. In this pod, we talk about the ins and outs of RAAS including: ✅ How RaaS works and why it’s…
Read More »