CyberSecurity
-
VMware

How To Install Tenable OT Security on Proxmox
In this video, I will demonstrates how to install Tenable OT’s core appliance on Proxmox. This new mini-series offers a detailed guide for setting up Tenable OT in a Proxmox environment, particularly helpful for those creating internal lab environments. I will cover everything from downloading the correct ISO from Tenable to configuring system requirements, network settings, and storage space. I…
Read More » -
Linux

#10 kali linux install on vmwere workstation pro – Ethical hacking @Auouymons
1. Purpose: • Kali Linux is primarily designed for cybersecurity professionals and ethical hackers to conduct security testing and vulnerability assessments. • It includes a comprehensive suite of tools for various security-related tasks, such as penetration testing, network analysis, forensics, and security research. 2. Features: • Kali Linux comes with a vast collection of open-source security tools and software, including…
Read More » -
Linux

Install CyberArk PSMP 14.2 on Rocky Linux 9.4
This video provides a comprehensive guide to installing CyberArk PSMP on Rocky Linux 9.4. We’ll walk you through: Preparing the server environment Installing the PSMP software Configuring the PSMP server Fixing the error with chkconfig not being installed which prevents the PSMP services from starting Running the script to Create-Recon-Logon.sh (Create the Logon and Recon user and add the recon…
Read More » -
workstation

Cybersecurity Tutorial | Cybersecurity for Beginners | Networking & Cryptography | Edureka
“🔥 Cyber Security Certification Course: 🔥 Certified Ethical Hacking Course | CEH v13 AI: 🔥 CompTIA Security (SY0-701) Exam: 🔥 CISSP Certification Training: In this *Cybersecurity Tutorial* , we’ll explore essential topics in cybersecurity, taking you from beginner concepts to advanced practices. This guide is designed to provide a strong foundation in cybersecurity, network security, and ethical hacking. Whether you’re…
Read More » -
Virtualization

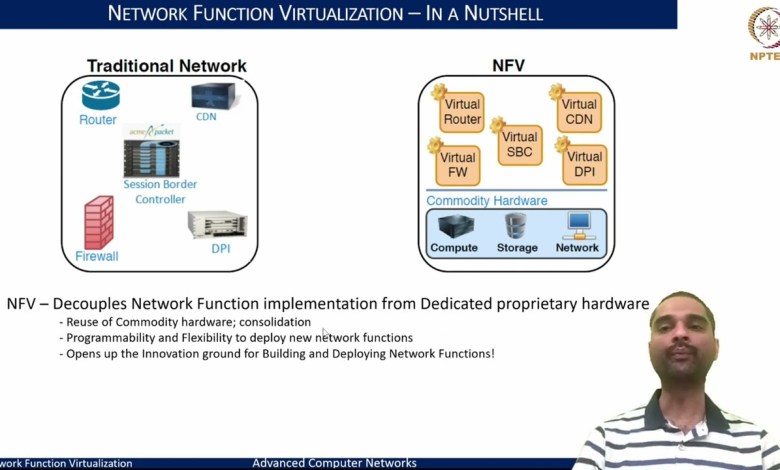
Lec-38 | Introduction to Network Function Virtualization – I #swayamprabha #CH30SP
Subject : Computer Science Course Name : Advanced Computer Networks 🌟 Welcome to Swayam Prabha! 🌟 Description: 🌐 Welcome to CH 30: IIT KHARAGPUR 02: Computer Sciences Engineering / IT & Related Branches and allied subjects ! Today, we’re diving into the world of Swayam Prabha, a revolutionary initiative offering 40 DTH channels dedicated to delivering high-quality educational programs 24/7…
Read More » -
workstation

Creating a Windows 10 Victim Machine (for Hackers) – Lec 09
Join me as I challenge myself to create a Kali Linux victim machine running Windows 10 on VMware and see if I can pull it off without any hiccups! Learn how to create a Kali Linux victim machine with Windows 10 on VMware in this step-by-step tutorial. This video is perfect for ethical hackers, penetration testers, and cybersecurity enthusiasts who…
Read More »