cybersecurity for beginners
-
Linux

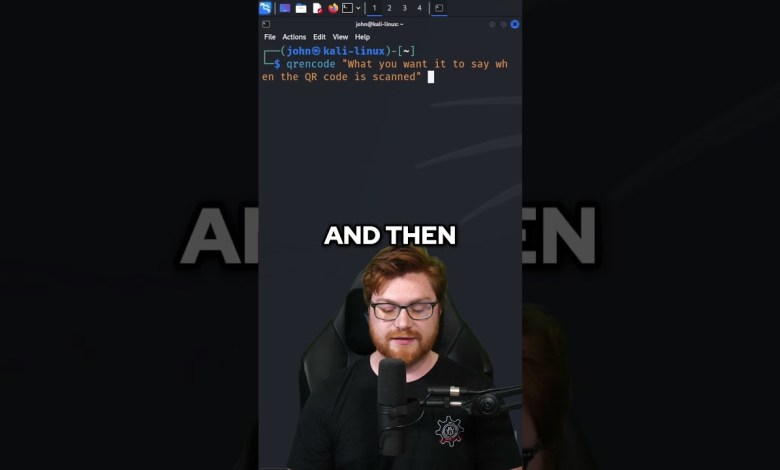
QR Codes on Linux
[ad_2] source
Read More » -
VMware

Practical Vulnerability Management using Qualys | Free Course for Security Analyst and GRC Analyst
Learn Practical Vulnerability Management using Qualys VM. 🔴 [FREE GUIDE] 7 Steps to get Cybersecurity Job in 90 days 👉🏻 Ultimate SOC Analyst Course learn.haxsecurity.com/services/security-analyst =========================== ⏰ Timecodes ⏰ =========================== 0:00 Introduction 0:33 Table of content 1:39 What is Qualys VM? 4:41 Architecture if Qualys VM 8:01 Practical Vulnerability Management 19:52 Setting up Qualys VM 21:10 Preparation 26:22 Knowledgebase 31:13…
Read More » -
VMware

Record-Breaking $75M Ransomware Heist
In this episode, the hosts discuss a news article about a Fortune 50 company that paid a record-breaking $75 million ransom to the Dark Angels ransomware gang. They express frustration with the current state of cybersecurity hiring and the need to attract talented individuals to the field. The hosts also highlight the importance of building security into organizations and the…
Read More » Windows Recall (was) a Security Nightmare
Learn Cybersecurity – Name Your Price Training with John Hammond: WATCH MORE: Dark Web & Cybercrime Investigations: Malware & Hacker Tradecraft: AmperageKit – Unlock Recall: ARM VM on Azure: Total Recall: 📧JOIN MY NEWSLETTER ➡ 🙏SUPPORT THE CHANNEL ➡ 🤝 SPONSOR THE CHANNEL ➡ 🌎FOLLOW ME EVERYWHERE ➡ ↔ ↔ ↔ ↔ 💥 SEND ME MALWARE ➡ 🔥YOUTUBE ALGORITHM ➡…
Read More »What is Attack Surface? Key Concepts for CC and CompTIA Security+ Success 2024
📚 Understanding Attack Surface for CC & Security+ Success 📚 Are you preparing for the CompTIA Security+ or CC exam? Understanding the attack surface is a crucial topic for your success. In this video, we break down what an attack surface is, why it matters, and how to manage it effectively. 🔥 What’s Covered in This Video: What is an…
Read More »11 TOOL 06: Installing and Configuring MetaSploitable Machine (Cyber Security Udemy Course for free)
11 TOOL 06: Installing and Configuring MetaSploitable Machine | Cyber Security Udemy Course for Free Welcome to the sixth tool in our free Cyber Security Udemy Course! In this video, we’ll guide you through the process of downloading, installing, and configuring the MetaSploitable machine. This intentionally vulnerable VM is perfect for practicing penetration testing and improving your ethical hacking skills.…
Read More »