cyber security
-
Microsoft

Phishing Resistant MFA for New Users in Microsoft 365
In this video, we dive into the world of Phishing Resistant Multi-Factor Authentication (MFA) for new users in Microsoft 365. Discover how to enhance your security using passkeys and Windows Hello for Business. Join us as we break down the steps to set up these powerful tools and keep your accounts safe from phishing attacks. Don’t miss out on these…
Read More » -
VMware

Firewalls Explained in 45 Seconds! 🔥 #Shorts #TechExplained #Viral
“Firewalls Explained in 45 Seconds! 🔥 #Shorts #TechExplained #Viral” firewall firewall explained palo alto firewall training firewall testing pfsense firewall fortinet firewall firewalls azure firewall basic firewall firewall basic firewall review paloalto firewall palo alto firewall how to build a virtual pfsense firewall in esxi palo alto firewall tutorial paloalto firewall training windows firewall firewall evasion configure firewall windows server…
Read More » -
Virtualization

Cloud and Virtualization Security – Guide to Network Security Fundamentals – CompTIA Security+
🌐 “Cloud and Virtualization Security – Guide to Network Security Fundamentals – CompTIA Security+” 🌐 Navigate the complexities of cloud and virtualization security with this in-depth guide, tailored for those pursuing CompTIA Security+ certification or any professional tasked with securing virtual environments. Explore Cloud Computing fundamentals, including the characteristics of clouds like On-demand Self-service, Immediate Elasticity, and Metered Services. Learn…
Read More » -
Hyper-v

14. Alessandro Magnosi: Leveraging Emulated Read-Only Filesystems and NTFS Glitches for Inf. & Pers.
What if Stuxnet was implemented nowadays? Join our talk as we explore this scenario, diving into strange NTFS weaknesses, emulated filesystem abuses, and modern cyber tactics. Discover how attackers could reshape a Stuxnet-like attack today, and how defenders can effectively defend against it. In homage to one of the most intricate cyberattacks ever recorded, our presentation titled “Resurrecting Stuxnet” explores…
Read More » -
Linux
![🎯 How to Install BeeLogger on Kali Linux | Create Undetectable Email Keyloggers! ⚡💻 [2024 Edition] 🎯 How to Install BeeLogger on Kali Linux | Create Undetectable Email Keyloggers! ⚡💻 [2024 Edition]](data:image/svg+xml;base64,PHN2ZyB4bWxucz0iaHR0cDovL3d3dy53My5vcmcvMjAwMC9zdmciIHdpZHRoPSI3ODAiIGhlaWdodD0iNDcwIiB2aWV3Qm94PSIwIDAgNzgwIDQ3MCI+PHJlY3Qgd2lkdGg9IjEwMCUiIGhlaWdodD0iMTAwJSIgc3R5bGU9ImZpbGw6I2NmZDRkYjtmaWxsLW9wYWNpdHk6IDAuMTsiLz48L3N2Zz4=)
🎯 How to Install BeeLogger on Kali Linux | Create Undetectable Email Keyloggers! ⚡💻 [2024 Edition]
Welcome to another exciting Ethical Hacking Tutorial! 🚀 In this video, I’ll walk you through the step-by-step process of installing and using the powerful BeeLogger tool on Kali Linux, showing you how to create undetectable keyloggers that send captured keystrokes directly to your email! 🕵️♂️📧 🌟 What You’ll Learn: 🛠 What is BeeLogger? Discover how this tool fits into the…
Read More » -
Linux

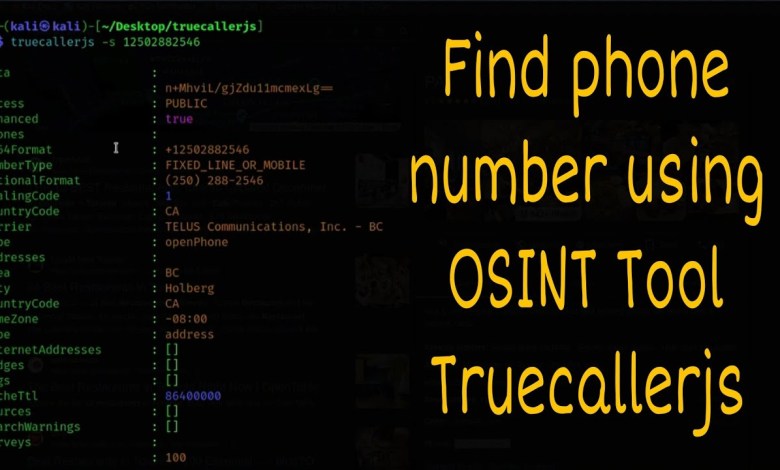
How to install OSINT tool Truecallerjs in Kali Linux
In this video, I will show you step-by-step how to install and run Osint tool Truecallerjs. Follow along with me and I hope you enjoy it (: If you know of any more OSINT tools interesting, let me know in the comment. [ad_2] source
Read More »


![🎯 How to Install BeeLogger on Kali Linux | Create Undetectable Email Keyloggers! ⚡💻 [2024 Edition] 🎯 How to Install BeeLogger on Kali Linux | Create Undetectable Email Keyloggers! ⚡💻 [2024 Edition]](https://wp.fifu.app/howto.goit.science/aHR0cHM6Ly9pLnl0aW1nLmNvbS92aS8tOXpPUk1Gd1RvNC9ocWRlZmF1bHQuanBn/83838deb86a0/%f0%9f%8e%af-how-to-install-beelogger-on-kali-linux-create-undetectable-email-keyloggers-%e2%9a%a1%f0%9f%92%bb-2024-edition.webp?w=780&h=470&c=1&p=608899)